FLOWTRIQ: SUB-SECOND DDOS MITIGATION FOR SAAS RESILIENCE
★The One-Second Margin: Why Instantaneous Mitigation is the New Security Standard
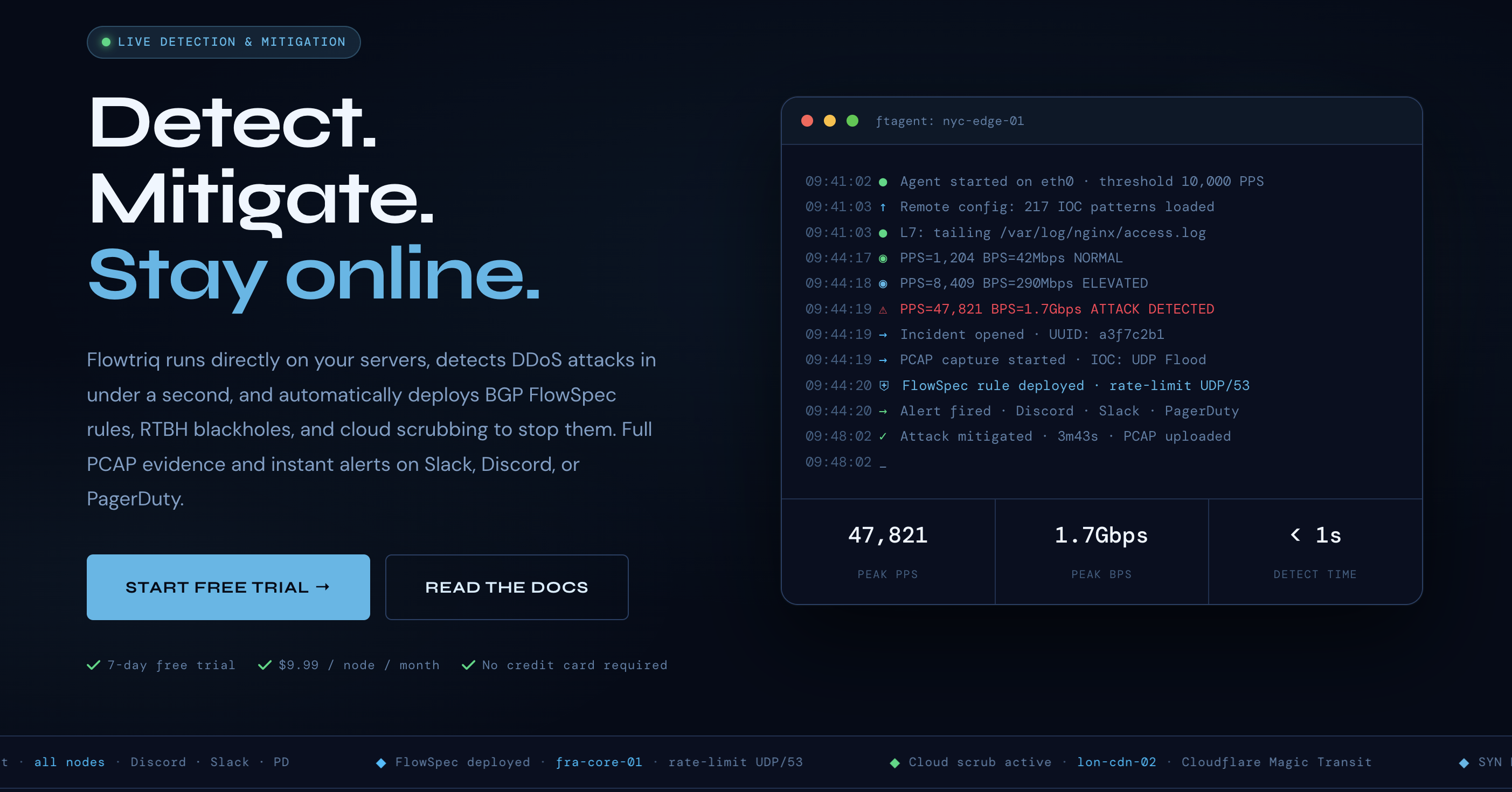
DDoS attacks now cost the average enterprise upwards of $6,000 per minute of downtime, yet the industry standard for detection and "time-to-mitigation" still lingers in the multi-minute range. Flowtriq is a lightweight, agent-based detection and auto-mitigation platform that shatters this latency by identifying and neutralizing threats in under one second. For SaaS leaders, this isn't just a technical upgrade; it’s the difference between a seamless user experience and a catastrophic churn event. The bottom line: if you aren't mitigating at the packet level in real-time, you aren't protecting your uptime—you're just documenting its demise.
★The Business Case: Resilience as a Revenue Driver
In my 15 years navigating the SaaS landscape, I’ve seen countless "slop" solutions that promise security but deliver nothing but alert fatigue and manual overhead. Flowtriq represents a shift toward what I call "Invisible Infrastructure." By deploying a Python-based agent (ftagent) directly on Linux servers, it bypasses the sluggishness of traditional out-of-band monitoring.
The ROI here is found in the preservation of Brand Equity. For a SaaS platform, a five-minute outage isn't just five minutes of lost productivity; it’s a breach of trust that triggers SLA credits and fuels competitor migrations. Flowtriq’s ability to learn traffic baselines dynamically means your DevOps team isn't wasting hundreds of hours on manual threshold tuning—a task that is notoriously prone to human error.
Furthermore, Flowtriq’s pricing model is a direct challenge to the "tax on growth" prevalent in the industry. At a flat $9.99 per node, it removes the financial unpredictability of traffic surcharges. In an era where CFOs are scrutinizing every line item for "SaaS sprawl," a predictable, high-performance security spend is a massive competitive advantage. You are essentially buying insurance that pays out in sub-second increments.
★Key Strategic Benefits
- Operational Efficiency: Flowtriq eliminates the "war room" culture by automating incident response through customizable runbooks. Instead of waking up an engineer at 3 AM to deploy BGP FlowSpec rules, the system executes pre-configured playbooks—chaining mitigation steps from local null-routing to cloud scrubbing—without human intervention.
- Cost Impact: By leveraging auto-escalation to providers like Cloudflare or Hetzner only when necessary, organizations can drastically reduce their spend on premium "always-on" cloud scrubbing services. You only engage the expensive pipes when the local agent confirms a legitimate breach.
- Scalability: The platform is built for the distributed age, allowing for multi-node management from a single pane of glass. Whether you are managing ten edge nodes or five hundred, the deployment remains a two-minute process, ensuring security posture scales linearly with your infrastructure.
- Risk Factors: While the agent is lightweight, any kernel-level interaction requires rigorous testing in staging environments to ensure no interference with proprietary application stacks. Additionally, leadership must ensure that "Auto-Mitigation" policies are finely tuned to prevent false positives from blocking legitimate, high-burst user traffic.
★Architecting the Rollout: Implementation Realities
Implementation of Flowtriq is refreshingly devoid of the "enterprise bloat" that plagues traditional security hardware. The ftagent is designed for rapid injection into existing CI/CD pipelines, requiring only a Linux environment and Python. From a change management perspective, the transition is low-friction because it complements, rather than replaces, existing stack components.
The initial 48 hours are critical; this is when the system’s dynamic baseline learning maps your "normal." I recommend a "Shadow Mode" phase where Flowtriq is permitted to detect and alert (via Slack or PagerDuty) but not yet execute BGP FlowSpec or RTBH blackholes. Once the accuracy of the detection—checked every single second at the PPS level—is verified against your specific traffic patterns, you can flip the switch to full auto-mitigation. This phased approach builds institutional trust in the automation before it takes the wheel.
★The Competitive Landscape
The DDoS mitigation market is currently split between "The Giants" and "The Niche Players." Flowtriq sits in a unique sweet spot by offering the sophisticated forensics of an enterprise appliance with the agility of a startup.
- Cloudflare: While Cloudflare remains the gold standard for global CDN-based protection, it can be an expensive "black box" for infrastructure-heavy providers. Flowtriq provides the granular, server-level PCAP data that Cloudflare often abstracts away.
- Akamai/Prolexic: These are high-touch, high-cost solutions suited for the Fortune 100. For the mid-market SaaS or the high-growth MSP, Flowtriq offers 90% of the utility at a fraction of the total cost of ownership.
- AWS Shield: For those locked into the Amazon ecosystem, AWS Shield is a logical choice, but it lacks the multi-cloud flexibility and sub-second local detection capabilities that Flowtriq’s agent provides across heterogeneous environments.
★Recommendation: The Path Forward
If your infrastructure team is still manually reacting to DDoS alerts, you are operating at a deficit. My recommendation for CTOs and VPs of Engineering is to initiate a 7-day trial on a non-critical edge node to validate the baseline learning accuracy. Move from "detection-only" to "automated-mitigation" within two weeks. In a sea of security mediocrity, Flowtriq is a high-signal tool that prioritizes packet-level truth over marketing fluff. Start by auditing your current "Time-to-Mitigation"—if it’s over 10 seconds, you need this.
✨ END OF BROADCAST ✨
🚀 READY TO EXPERIENCE THE FUTURE?
VISIT FLOWTRIQ →